Resume Basics and Foundation
Before you ask anyone to review your resume, make sure you've covered the basics. These are the things that get people filtered out before a human ever reads their work.
Career Advice: 7 Things They Don’t Teach You In School
I realized there was so much I want to share with the next generation of pros. From the dangers of tying your identity to your job to the "millions left on the table" due to a lack of financial literacy, here are the seven pieces of advice I give to anyone looking to build a sustainable, successful career in this industry.
Communication Challenges in Cybersecurity
Early in my career, the consistent feedback was that I needed to improve my communications…I was "too blunt" or "too harsh." It took years to understand what was missing. Now, I realize effective security communication requires translating technical details into business terms and recognizing the power of unconscious bias.
The core lesson? Speaking in the language of your listener builds trust, and communicating trade-offs builds influence.
How to Prepare for Layoffs: Lessons From My First Time
“Nothing truly prepares you for it.” Here’s the short list of prep and response moves that softened the blow for me and can for you.
The Reality of Phishing Simulations
Yes, your users are susceptible. I am. Everyone is.” Here’s how to turn tests into better outcomes.
How to Think About Risk in Generative AI: It’s Not As New As You Think
If you’re dealing with third-party GenAI, the risk boils down to deliberate governance you already know how to do.
Defending Against Scattered Spider
Sophisticated ops, simple strategy. Fix the fundamentals in identity and detection to reduce risk in these campaigns.
Why Top Talent Leaves
Exploring reasons why top talent leaves and organization and the cultural aspects that are essential for them to excel.
SEC Cyber Incident Materiality Disclosure Rule
This isn’t a massive change; this is a massive chance to help your organization define a process that establishes cybersecurity as a business partner and for us to show the business leaders in our orgs that we are prepared to truly be partners.
Leadership Culture
Ultimately my role as a leader is to ensure that teams have the tools and expectations they need to do their job and to remove roadblocks preventing them from being successful.
Responding To Ransomware - A Pragmatic Guide
There is no one size fits all for ransomware response, but there are some universal concepts that I have seen work effectively.
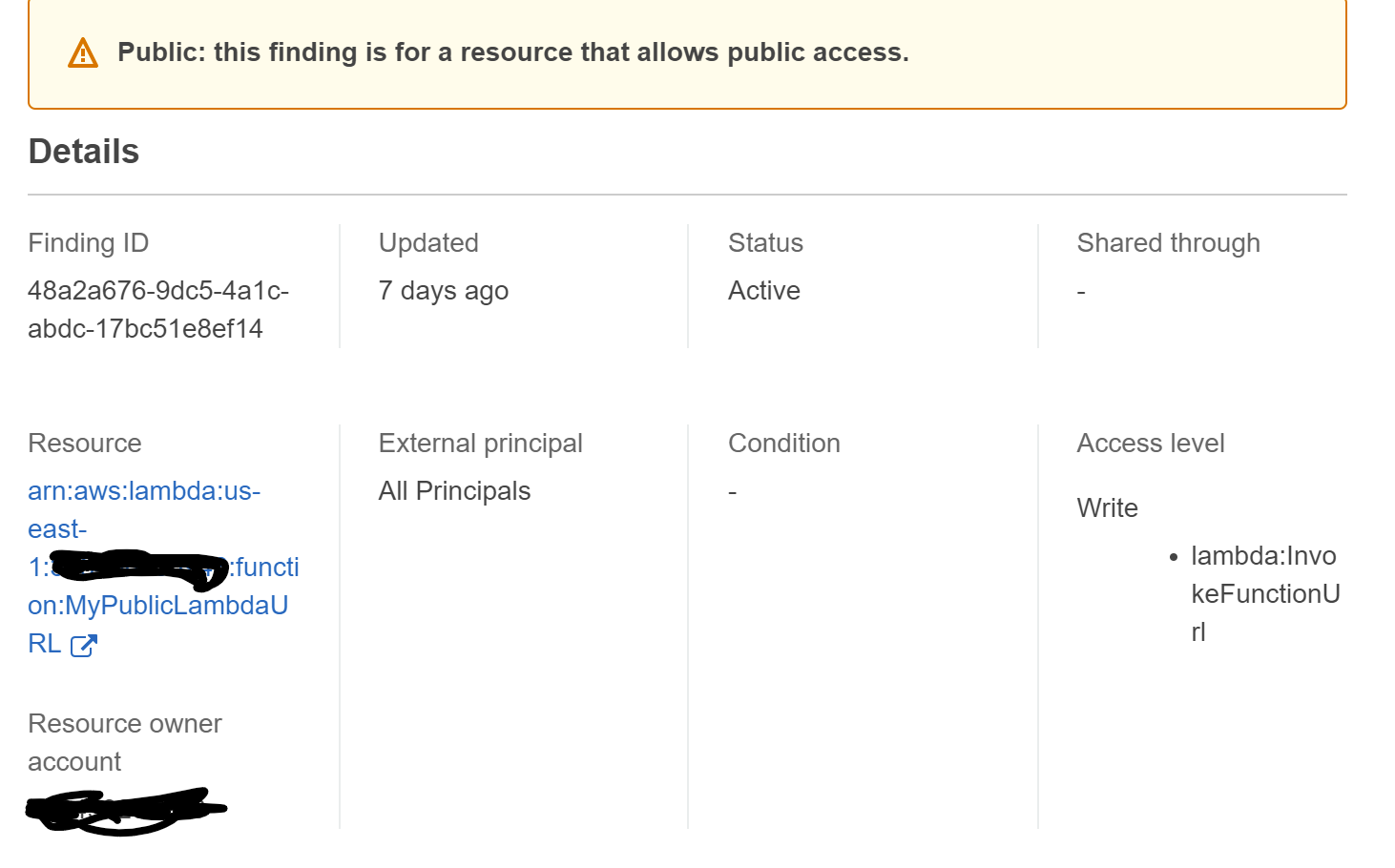
AWS Lambda Function URL
What should we do about this new feature in Lambda? Allow it? Prevent it?
Identity Theft - It Happened To Me
My account of identify theft and steps I took before and after.
Am I Secure From Ransomware?
Are you protected from ransomware? How can you tell? If you wanted to know your ransomware risk, what would you look for?
Log4Shell / Log4j Explained - Details and References
Everything you need to know about Log4Shell
New Job, Pandemic, Fully Remote
The bottom line is this. Starting at a new organization remotely is not hard, but to do it well takes effort.
Be purposeful and genuine in conversation.
Use “I” a lot less.
Ask lots of questions
Get to know people. For real.
Show your face. Use quality tech.